Reading Time: 4 minutesThe Chief Data Officer (CDO) role has shifted from a defensive, risk-focused function to an offensive, value-creating business leader. The 2025 mandate is to align every data initiative with measurable business outcomes.
Meeting of Brilliant Syche – IT Pro's Corner

Reading Time: 4 minutesThis document provides a condensed, actionable summary of the comprehensive blueprint for formalizing an enterprise digital marketing strategy. It integrates leading planning frameworks (SOSTAC®, RACE), governance models, technology architecture, and performance measurement to guide the shift from ad-hoc tactical execution to a strategic, governed, and data-driven marketing function.

Reading Time: 3 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: 2024-07-25 Version: 1.0 Part 1: Strategic Foundations 1.1 Defining the Modern Marketing Management Suite (MMS) A modern MMS is an integrated platform that has Read More …

Reading Time: 4 minutesInformation Technology (IT) governance has evolved from a technical control function into a strategic enterprise imperative, driven by digital transformation, complex regulations, and escalating cybersecurity threats. The modern mandate for IT governance is to ensure technology aligns with business strategy, delivers measurable value, optimizes resources, and manages risk effectively.

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: August 19, 2024 Location: Dhaka, Bangladesh Version: 1.0 Part I: The Strategic Imperative of Digital Business A formal digital business strategy is a roadmap Read More …

Reading Time: 4 minutesIn an era of unprecedented volatility, IT Resilience is a fundamental requirement for survival, moving beyond reactive Disaster Recovery (DR) and Business Continuity (BC) to a proactive discipline of survivability. This blueprint provides a framework to embed resilience into the core of the digital enterprise, ensuring critical services remain available despite adverse conditions.

Reading Time: 7 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: June 13, 2025 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary This blueprint provides a comprehensive guide for achieving and maintaining PCI DSS 4.0 Read More …

Reading Time: 7 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 28, 2024 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary The Sherwood Applied Business Security Architecture (SABSA) is a foundational, open-standard methodology for Read More …

Reading Time: 3 minutesPart I: The Strategic Imperative The adoption of enterprise blockchain, or Distributed Ledger Technology (DLT), is driven by the need for enhanced trust, transparency, and efficiency in multi-party business processes. Unlike public blockchains (e.g., Bitcoin), enterprise systems are permissioned, meaning Read More …

Reading Time: 3 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: March 1, 2025 Version: 1.0 Part 1: The Strategic Imperative The shift from traditional, script-based automation to AI-driven quality engineering is a transformative evolution Read More …

Reading Time: 3 minutesThe selection of an enterprise server platform is a foundational IT decision, impacting agility, security, and cost for years. This blueprint analyzes the physical server offerings from Dell Technologies, Hewlett Packard Enterprise (HPE), IBM, and Cisco Systems, moving beyond feature lists to evaluate core philosophies and long-term value.
Reading Time: 4 minutesThe management of enterprise content has evolved from a back-office archival function into a strategic driver of digital transformation. The market has shifted from traditional, monolithic Enterprise Content Management (ECM) systems to flexible Content Services Platforms (CSPs), and now to the era of Intelligent Content Automation.

Reading Time: 3 minutesThe traditional “castle-and-moat” security model is obsolete, broken by the rise of cloud computing, a hybrid workforce, and the explosion of unmanaged devices. The network perimeter has dissolved, creating a new reality where attackers with compromised credentials can move freely within a supposedly “trusted” internal network.

Reading Time: 3 minutesThe enterprise firewall has evolved from a perimeter gatekeeper into a distributed, strategic enforcement point for modern hybrid networks. The selection of a Next-Generation Firewall (NGFW) platform is a foundational decision, dictating network architecture, operational models, and long-term security posture.

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: January 21, 2025 Location: Dhaka, Bangladesh Version: 1.0 Part I: The Strategic Mandate of the Modern CTO The role of the Chief Technology Officer Read More …

Reading Time: 3 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: January 21, 2025 Location: Dhaka, Bangladesh Version: 1.0 1. Core Concept: The “Goldilocks” Architecture The Micro-Monolith (or Modular Monolith) is a software architecture that Read More …
Reading Time: 3 minutesThe selection of a Security Information and Event Management (SIEM) platform is a foundational decision for any modern Security Operations Center (SOC). The modern SIEM has evolved from a simple log repository into an intelligent, AI-driven platform essential for digital resilience.

Reading Time: 4 minutesISO/IEC 27001 is the international standard for establishing, implementing, maintaining, and continually improving an Information Security Management System (ISMS). The core objective of an ISMS is to protect the Confidentiality, Integrity, and Availability (CIA Triad) of an organization’s information assets.

Reading Time: 3 minutesApplication Portfolio Management (APM) is a strategic discipline for managing an enterprise’s software applications as a portfolio of assets. The Gartner TIME Model is the industry-standard framework for this process, enabling organizations to make data-driven decisions to optimize costs, reduce risk, and align IT investments with business objectives.
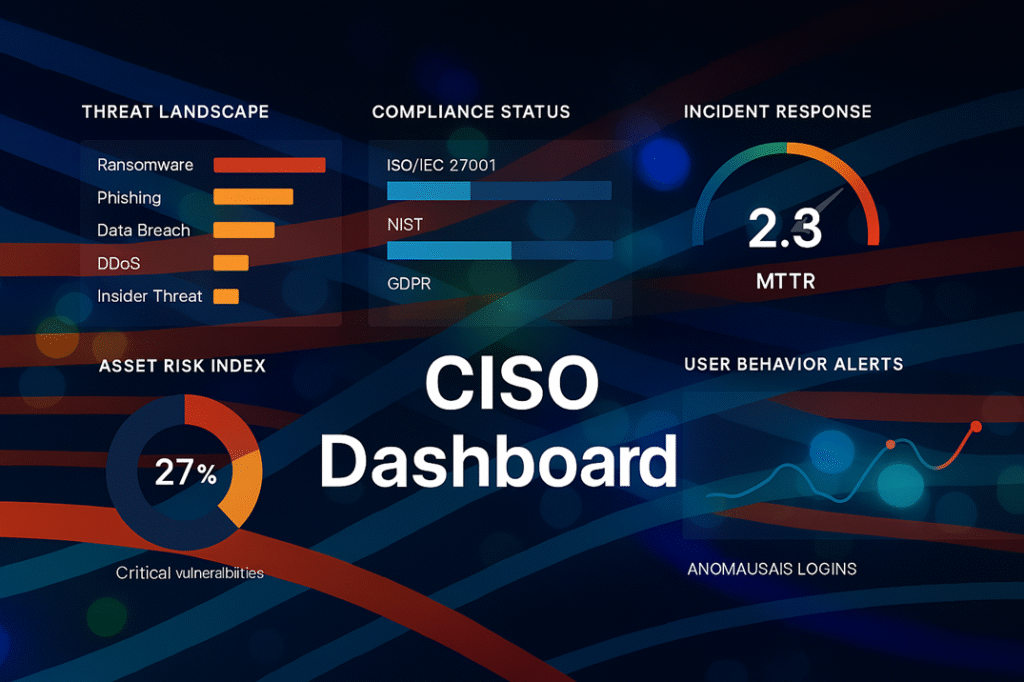
Reading Time: 3 minutesThe modern Chief Information Security Officer (CISO) has evolved from a technical manager into a strategic business leader. In an era of enterprise-wide digital transformation, the CISO’s primary mandate is to architect digital trust, enabling secure business growth while managing cyber risk.
Reading Time: 4 minutesThe Tensor Processing Unit (TPU) is a custom-built Application-Specific Integrated Circuit (ASIC) developed by Google to accelerate AI and machine learning workloads. Its creation was driven by the unsustainable computational and energy demands of running deep neural networks on general-purpose hardware like CPUs and GPUs.

Reading Time: 4 minutesThe management of endpoint devices has evolved from a tactical IT function into a strategic imperative. This evolution reflects the changing nature of work, from simple Mobile Device Management (MDM) to comprehensive Enterprise Mobility Management (EMM), and now to a unified approach.

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: February 3, 2022 Location: Dhaka, Bangladesh Version: 1.0 Part I: The Strategic Imperative of Data Integrity 1.0 Defining the Data Integrity Landscape Data integrity Read More …

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: September 4, 2023 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary: The Data Imperative In the modern economy, data is the central force behind competitive Read More …