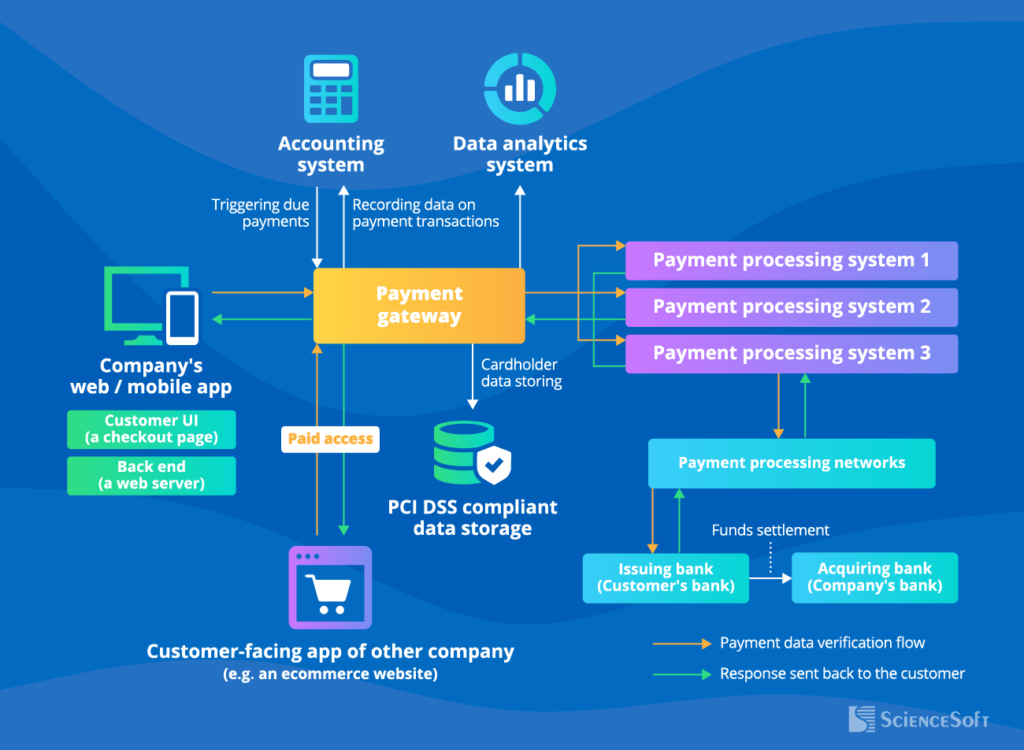
Reading Time: 2 minutesA payment gateway is a secure interface that facilitates online transactions by acting as a bridge between customers, merchants, and financial institutions. It ensures the secure transfer of payment data, processes transactions, and communicates the results back to the merchant’s system. Payment gateways are integral to e-commerce platforms, enabling seamless and secure payment experiences.