Reading Time: 2 minutesHID MIFARE DESFire technology, particularly the DESFire EV3, offers advanced security features and flexibility for various applications, including access control and smart city services.
Meeting of Brilliant Syche – IT Pro's Corner

Reading Time: 3 minutesn 2026, the world’s most secure phones range from mass-market flagships with long-term support to specialized devices featuring hardware kill switches and military-grade encryption. For the average user, the Google Pixel 10 Pro XL and Apple iPhone 17 Pro Max offer the best balance of usability and security, while privacy purists often prefer the Purism Librem 5 for its physical hardware controls.
Reading Time: 3 minutesCybersecurity leadership is no longer optional—it’s a board-level priority. As digital threats escalate and compliance frameworks tighten, organizations face a critical decision: should they appoint a full-time, in-house Chief Information Security Officer (CISO) or engage a Virtual CISO (vCISO) for flexible, outsourced expertise?
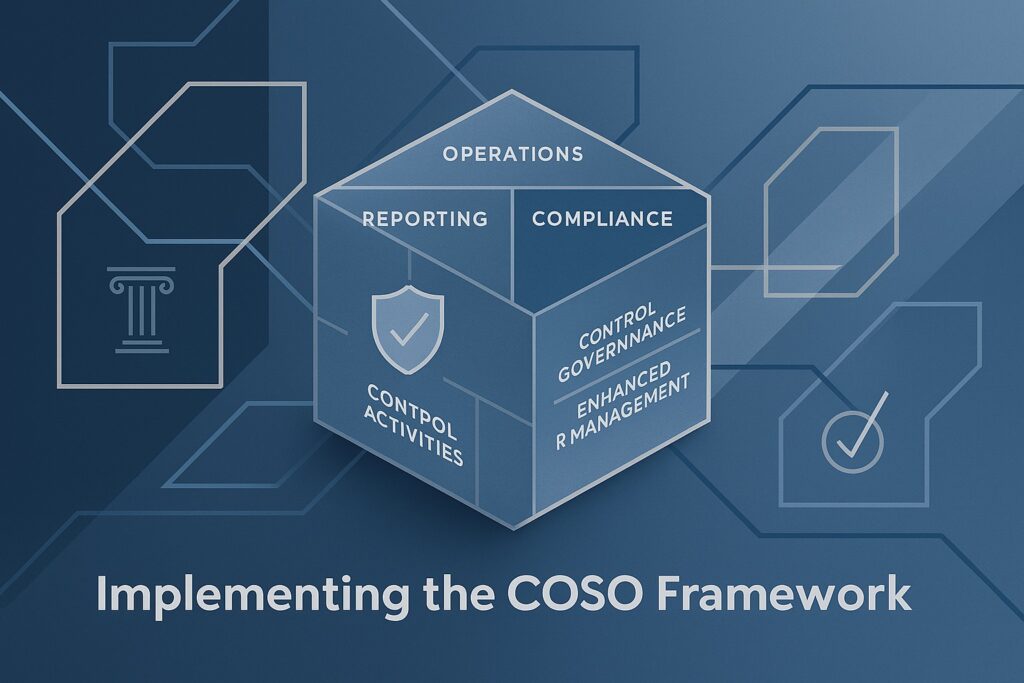
Reading Time: 5 minutesUnderstand the significance of the COSO framework in your organization’s internal control strategy for improved governance, risk management, and compliance measures. In today’s complex business environment, organizations face a multitude of risks ranging from financial misstatement and operational inefficiencies to Read More …

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: September 12, 2025 Location: Dhaka, Bangladesh Version: 1.0 The paradigm for securing enterprise cloud environments is undergoing a fundamental transformation. Traditional, siloed security tools Read More …

Reading Time: 3 minutesDetection‑as‑Code (DaC) is moving from niche practice to mainstream SOC engineering discipline. By embedding detection logic into CI/CD‑style pipelines, organizations are achieving faster deployment cycles, higher detection accuracy, and measurable reductions in false positives.

Reading Time: 2 minutesAI-driven tools can craft highly targeted, multilingual phishing emails by scraping OSINT, leaked credentials, and social media profiles. Deepfake voice generators mimic executives’ tone and emotional cues, making human detection far more difficult. Services like PhishGPT+ enable automated spear-phishing campaigns tailored by geolocation, language, and psychological triggers.

Reading Time: 5 minutesStatus: Final BlueprintAuthor: Shahab Al Yamin ChawdhuryOrganization: Principal Architect & Consultant GroupResearch Date: April 2, 2025Location: Dhaka, BangladeshVersion: 1.0 1. Executive Summary and Strategic Imperatives The “SOAR Playbook for Malware Containment” outlines Security Orchestration, Automation, and Response (SOAR) as a Read More …

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: March 15, 2025 Location: Dhaka, Bangladesh Version: 1.0 Table of Contents 1. Executive Summary This “SOAR Playbook for Ransomware” offers a comprehensive blueprint for Read More …

Reading Time: 5 minutesThe escalating volume and sophistication of cyber threats, coupled with a shortage of security professionals, necessitate a shift from manual incident response (IR) to automated solutions. Security Orchestration, Automation, and Response (SOAR) platforms offer a transformative approach by consolidating security operations, automating repetitive tasks, and streamlining incident handling.

Reading Time: 5 minutesThis blueprint provides a comprehensive framework for preparing for, responding to, and recovering from ransomware attacks. It emphasizes cyber resilience as a strategic imperative, integrating proactive defense, swift incident response, and continuous improvement to minimize impact and ensure business continuity.

Reading Time: 6 minutesData Loss Prevention (DLP) is a crucial cybersecurity strategy designed to detect and prevent data breaches by blocking unauthorized extraction or exposure of sensitive data. It combines people, processes, and technology to identify, classify, and apply usage policies to sensitive information across endpoints, networks, and cloud platforms (data at rest, in motion, and in use).

Reading Time: 6 minutesExtended Detection and Response (XDR) is a pivotal evolution in enterprise cybersecurity. It unifies, intelligently, and automates threat detection, investigation, and response by aggregating telemetry from endpoints, networks, cloud, identity, and email into a single platform. This holistic visibility, powered by AI/ML, detects complex attacks, reduces alert fatigue, and accelerates incident containment.
Reading Time: 7 minutesCybersecurity assessment frameworks are structured methodologies guiding organizations to establish and maintain robust cybersecurity postures. They provide a roadmap for identifying, assessing, and managing risks to digital assets, enhancing resilience, streamlining operations, and building trust. Cybersecurity is a core business enabler, requiring agile, adaptive security, strong governance, and leveraging a complementary ecosystem of frameworks to tailor security to unique needs.
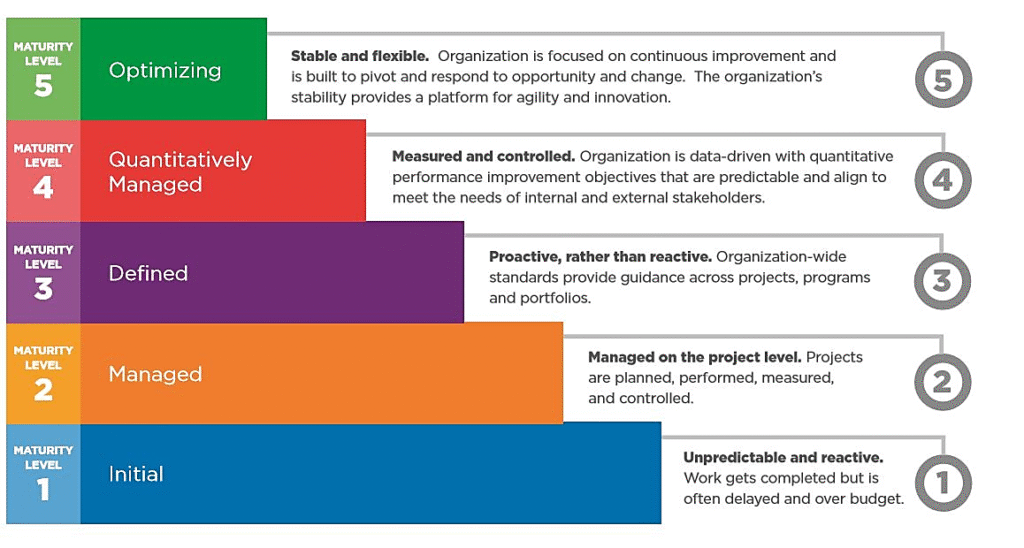
Reading Time: 4 minutesThis document provides a concise overview of the “Implementation Plan – SOC-CMM” research blueprint, synthesizing key insights for establishing, maturing, and optimizing Security Operations Center (SOC) capabilities. It highlights the core framework, implementation lifecycle, and critical areas for optimization across people, processes, technology, performance, and compliance.
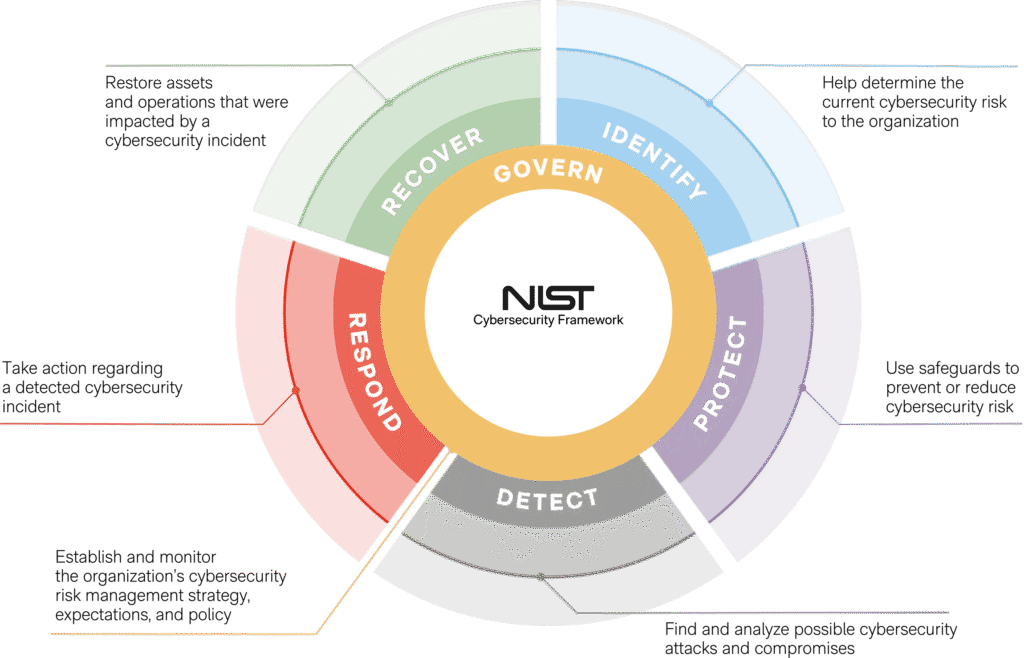
Reading Time: 5 minutesThis blueprint outlines a strategic and actionable plan for implementing the NIST Cybersecurity Framework (CSF) 2.0, the leading global standard for managing cyber risk. It emphasizes a proactive, governance-driven approach to enhance organizational resilience, optimize resource allocation, and streamline compliance, transforming cybersecurity into a core business enabler.

Reading Time: 6 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: March 17, 2025 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary The “Implementation Plan – NIST AI RMF” provides a comprehensive roadmap for large enterprises Read More …

Reading Time: 4 minutesThis document provides a condensed, actionable summary of the comprehensive blueprint for formalizing an enterprise digital marketing strategy. It integrates leading planning frameworks (SOSTAC®, RACE), governance models, technology architecture, and performance measurement to guide the shift from ad-hoc tactical execution to a strategic, governed, and data-driven marketing function.

Reading Time: 4 minutesInformation Technology (IT) governance has evolved from a technical control function into a strategic enterprise imperative, driven by digital transformation, complex regulations, and escalating cybersecurity threats. The modern mandate for IT governance is to ensure technology aligns with business strategy, delivers measurable value, optimizes resources, and manages risk effectively.

Reading Time: 7 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: June 13, 2025 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary This blueprint provides a comprehensive guide for achieving and maintaining PCI DSS 4.0 Read More …

Reading Time: 7 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 28, 2024 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary The Sherwood Applied Business Security Architecture (SABSA) is a foundational, open-standard methodology for Read More …

Reading Time: 3 minutesPart I: The Strategic Imperative The adoption of enterprise blockchain, or Distributed Ledger Technology (DLT), is driven by the need for enhanced trust, transparency, and efficiency in multi-party business processes. Unlike public blockchains (e.g., Bitcoin), enterprise systems are permissioned, meaning Read More …

Reading Time: 3 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: March 1, 2025 Version: 1.0 Part 1: The Strategic Imperative The shift from traditional, script-based automation to AI-driven quality engineering is a transformative evolution Read More …

Reading Time: 3 minutesThe selection of an enterprise server platform is a foundational IT decision, impacting agility, security, and cost for years. This blueprint analyzes the physical server offerings from Dell Technologies, Hewlett Packard Enterprise (HPE), IBM, and Cisco Systems, moving beyond feature lists to evaluate core philosophies and long-term value.

Reading Time: 3 minutesThe traditional “castle-and-moat” security model is obsolete, broken by the rise of cloud computing, a hybrid workforce, and the explosion of unmanaged devices. The network perimeter has dissolved, creating a new reality where attackers with compromised credentials can move freely within a supposedly “trusted” internal network.

Reading Time: 3 minutesThe enterprise firewall has evolved from a perimeter gatekeeper into a distributed, strategic enforcement point for modern hybrid networks. The selection of a Next-Generation Firewall (NGFW) platform is a foundational decision, dictating network architecture, operational models, and long-term security posture.

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: January 21, 2025 Location: Dhaka, Bangladesh Version: 1.0 Part I: The Strategic Mandate of the Modern CTO The role of the Chief Technology Officer Read More …
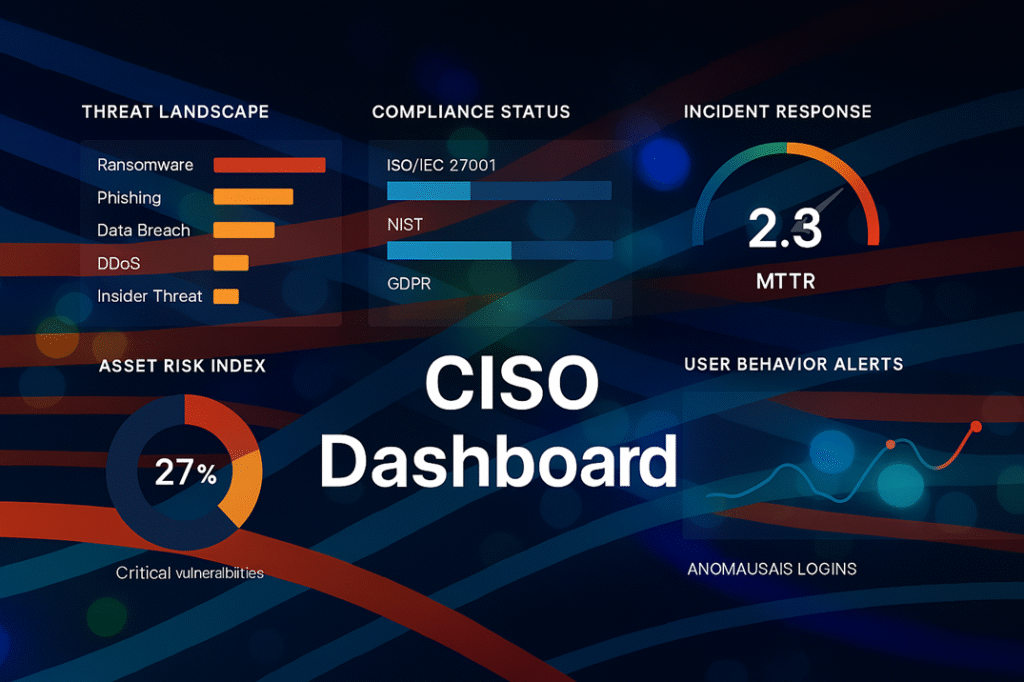
Reading Time: 3 minutesThe modern Chief Information Security Officer (CISO) has evolved from a technical manager into a strategic business leader. In an era of enterprise-wide digital transformation, the CISO’s primary mandate is to architect digital trust, enabling secure business growth while managing cyber risk.

Reading Time: 4 minutesThe management of endpoint devices has evolved from a tactical IT function into a strategic imperative. This evolution reflects the changing nature of work, from simple Mobile Device Management (MDM) to comprehensive Enterprise Mobility Management (EMM), and now to a unified approach.

Reading Time: 6 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: June 1, 2024 Location: Dhaka, Bangladesh Version: 1.0 1. The Core Dilemma: Assessor vs. Builder Mindset We are observing worldwide adoption on CISSP Read More …