
Reading Time: 3 minutesThe decision to build a security platform from open-source components is conditional.
Meeting of Brilliant Syche – IT Pro's Corner

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 26, 2024 Version: 1.0 1. The Strategic Imperative for Modernization Application modernization is a critical business initiative to update legacy software, aligning it Read More …

Reading Time: 6 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: June 1, 2024 Location: Dhaka, Bangladesh Version: 1.0 1. The Core Dilemma: Assessor vs. Builder Mindset We are observing worldwide adoption on CISSP Read More …

Reading Time: 3 minutesStatus: Final Blueprint Summary Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: February 22, 2024 Location: Dhaka, Bangladesh Version: 1.0 1. The Strategic Imperative for Integrated Resilience The modern business landscape demands a proactive, integrated Read More …
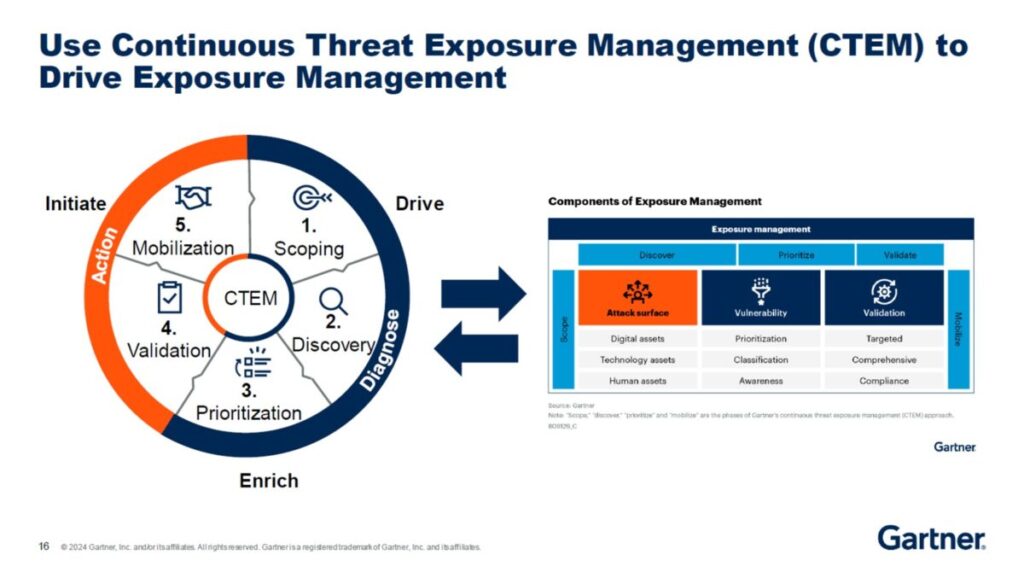
Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 23, 2025 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary Continuous Threat Exposure Management (CTEM) marks a strategic evolution from reactive, incident-driven security to Read More …

Reading Time: 5 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: September 23, 2023 Location: Dhaka, Bangladesh Version: 1.0 1.0 Executive Summary: Beyond Consolidation Unified virtual machine (VM) management has evolved from simple hypervisor consolidation Read More …
Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 21, 2024 Location: Dhaka, Bangladesh Version: 1.0 1.0 Executive Summary 2.0 The Evolving Threat Landscape 3.0 Amplified Risk Factors in Hybrid Environments 4.0 Read More …

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 21, 2025 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary 2. Deep Dive: Laravel-Specific Concerns for Enterprise Use 3. Deep Dive: MySQL-Specific Concerns Read More …

Reading Time: 8 minutesExecutive Summary The advent of publicly available generative Artificial Intelligence (AI) represents a paradigm shift in the cybersecurity landscape. While offering immense productivity benefits, these tools have also been weaponized, providing adversaries with the means to automate, scale, and enhance Read More …

Reading Time: 5 minutes1.0 Executive Summary This document provides a comprehensive architectural blueprint for the strategic implementation of honeypots within an enterprise network. Honeypots serve as a proactive defense mechanism, acting as decoy systems designed to attract, deceive, and analyze the activities of Read More …

Reading Time: 4 minutesTable of Contents 1. Executive Summary Enterprises embracing two or more public clouds face unique security challenges: inconsistent controls, blind spots, and operational complexity. This report outlines a holistic architecture—spanning network fabric, resilient application platforms, identity-centric access, client-specific handling, and Read More …

Reading Time: 3 minutesMachine Identity Security (MIS) or Machine Identity Management (MIM) is another critical aspect of cybersecurity that focuses on securing and managing the digital identities of machines, such as servers, applications, and IoT devices, which is currently overlooked due to lack Read More …
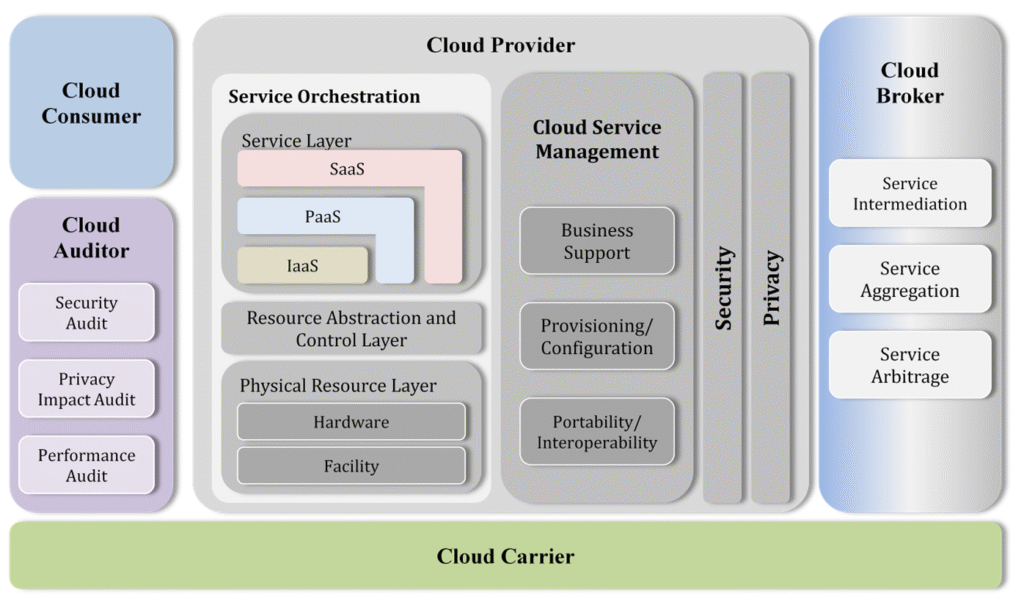
Reading Time: 9 minutesImage Source: https://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication500-292.pdf Cloud computing has become an integral part of modern IT infrastructure, enabling enterprises to achieve scalability, efficiency, and agility. This paper discusses the Cloud Computing Reference Architecture (CCRA), including its key adoption requirements, standard bodies of knowledge Read More …
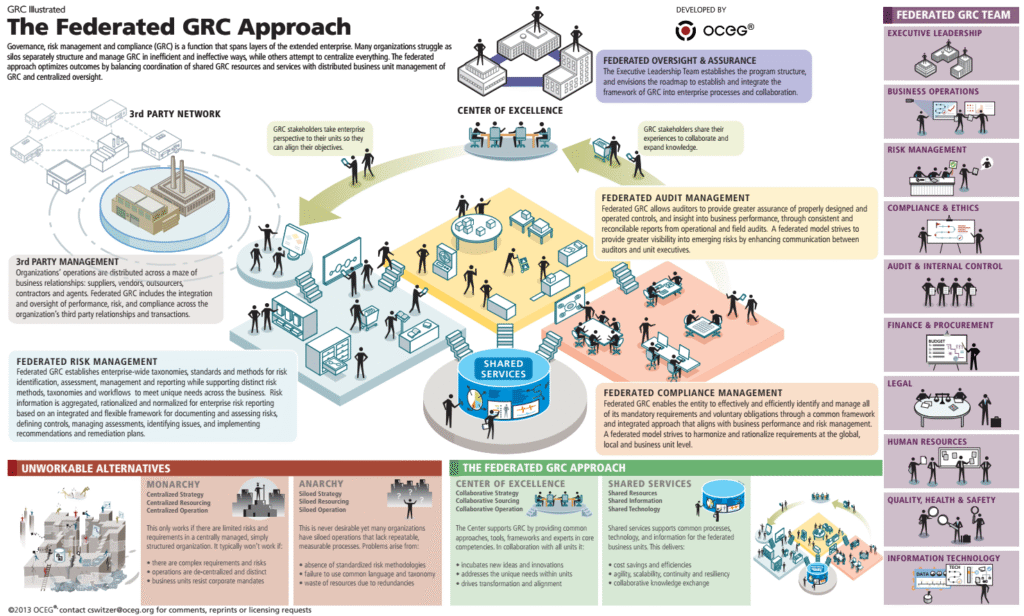
Reading Time: 3 minutesImage source: OCEG Organizations face unprecedented challenges in governance, risk management, and compliance (GRC). The increasing complexity of risks, regulations, and operational demands necessitates a modern, integrated approach to GRC. To connect the dots between risks, compliance, and other GRC elements that Read More …
Reading Time: 2 minutesCISO due diligence refers to the process a CISO (Chief Information Security Officer) and their team conduct to assess the cybersecurity posture and practices of an organization or third party, particularly during mergers and acquisitions, or before entering into a Read More …
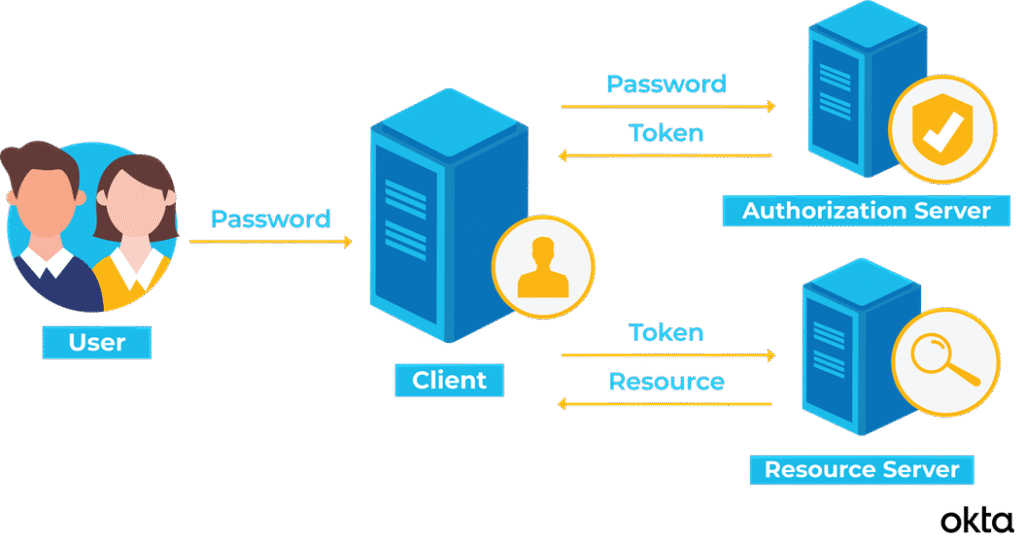
Reading Time: 4 minutesImage Source: TokenBasedAuthentication2.png (3121×1648) Developing an authentication server is a crucial part of building secure applications. Here’s a structured approach to creating one: 1. Define Your Authentication Method: Decide whether you’ll use: 2. Choose a Tech Stack: Pick a language Read More …

Reading Time: 5 minutesImage Source: What is OAuth? (An Introduction to OAuth and OpenID) – The Genius Blog OAuth 2.0 is a widely used authorization framework that enables secure access to resources without exposing user credentials. Here’s a breakdown of its architecture, possibilities Read More …
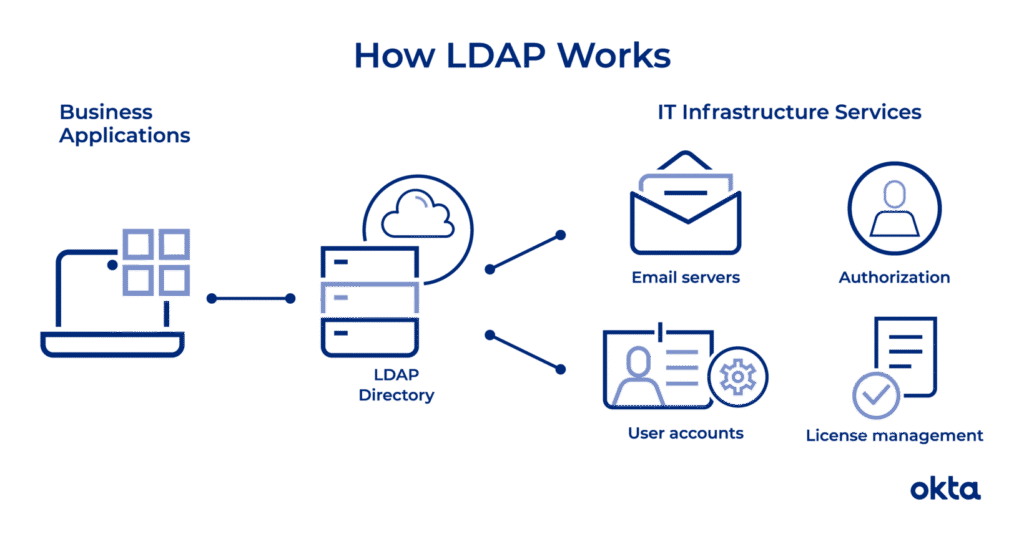
Reading Time: 2 minutesImage Source: https://www.okta.com/identity-101/what-is-ldap/ The Lightweight Directory Access Protocol (LDAP) is an open, vendor-neutral, industry-standard application protocol for accessing and maintaining distributed directory information services over an Internet Protocol (IP) network. LDAP is based on a simpler subset of the standards Read More …

Reading Time: 4 minutesIntroduction In an era where cybersecurity threats are growing in complexity, organizations must continually adapt their security measures to protect sensitive information. Privileged Access Management (PAM) plays a critical role in safeguarding access to high-level accounts that control systems and Read More …
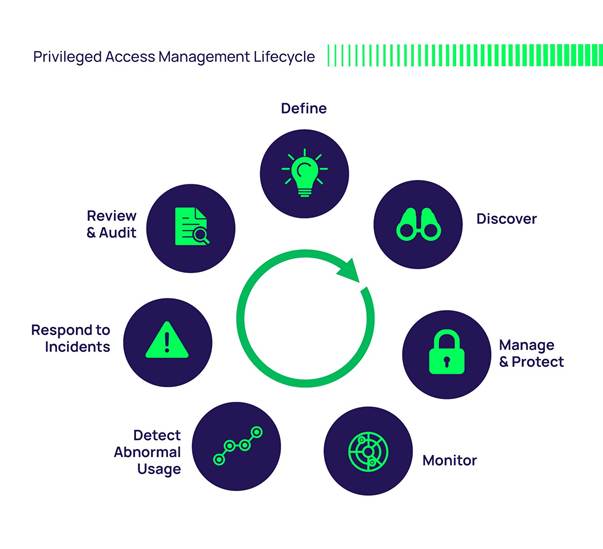
Reading Time: 2 minutesPAM organizes the key aspects of securing high-privilege accounts and activities. It typically includes core functionalities like discovery, control, password management, session monitoring, and compliance, along with components like account discovery, access management, and password vault. The mindmap helps understand Read More …

Reading Time: 3 minutes1. Introduction With the increasing threats to online security, securing personal blogs is not just about maintaining content integrity but also ensuring protection against cyberattacks and compliance with global data privacy laws. This paper explores essential security mechanisms and compliance Read More …

Reading Time: 3 minutesBackground: with an increasing demand for reliable internet services in Bangladesh, a twenty years ofd ISP aimed to differentiate itself by providing high-quality, affordable services while ensuring efficient operations and scalability. To achieve these goals, Enterprise Architecture (EA) was implemented Read More …
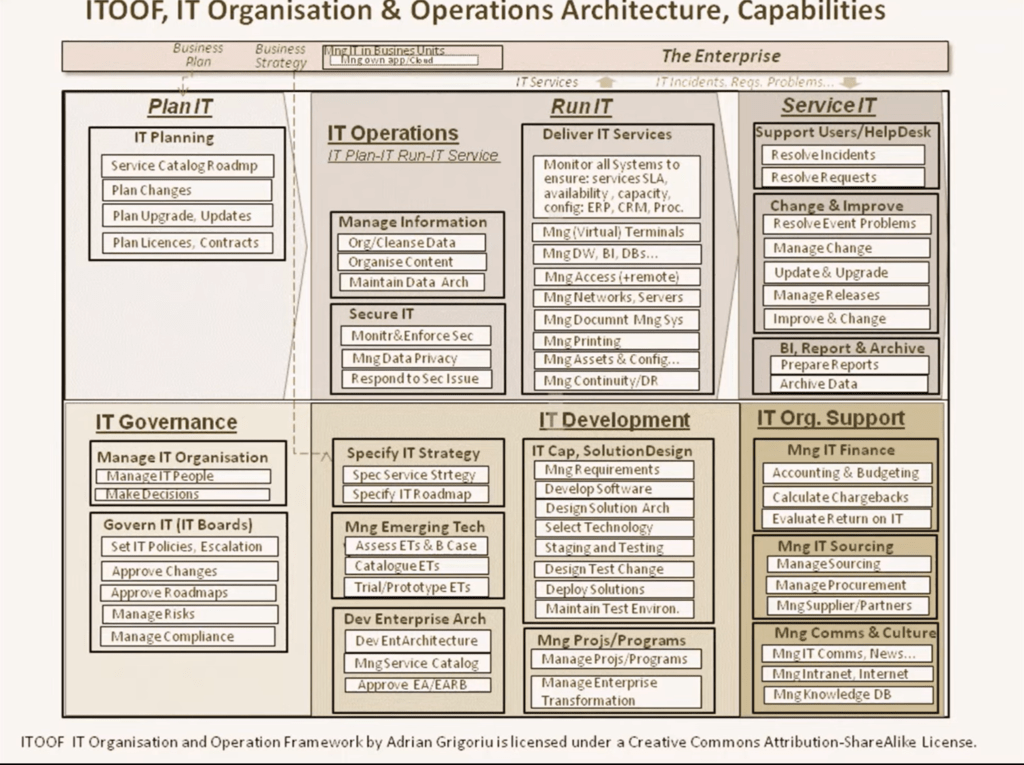
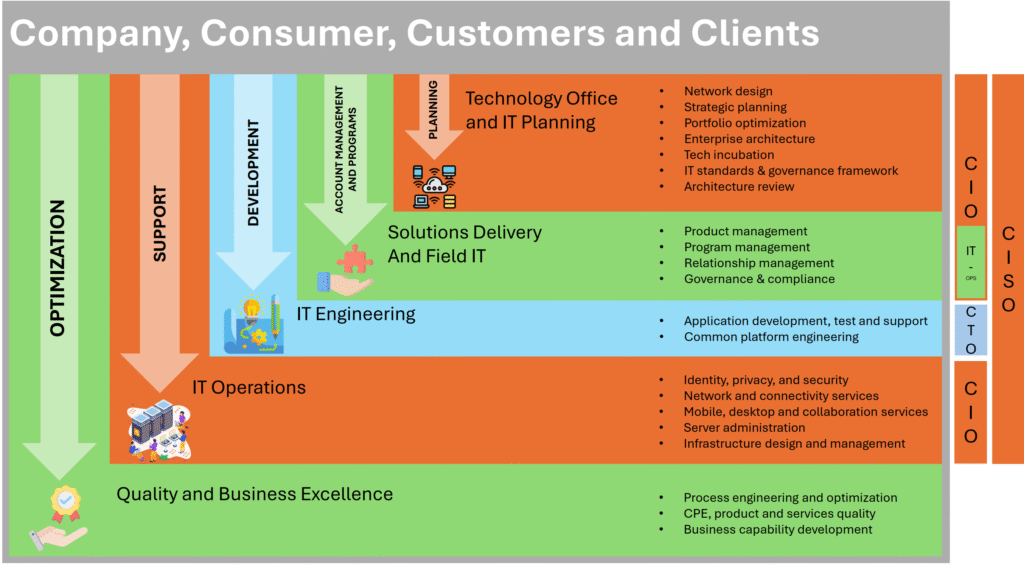
Reading Time: 2 minutesQUOTED FROM THE VIDEO from YouTube by Adrian Grigoriu “The ITOOF, or IT Operation and Organization Framework, is an IT Service Management (ITSM) framework designed to help plan, build, organize, and describe the organization and operation of an IT department. Read More …

Reading Time: 3 minutesIn today’s rapidly evolving digital landscape, organizations face an ever-increasing threat of cyberattacks. To fortify their defenses, they must adopt a comprehensive approach that combines industry standards, advanced detection mechanisms, and proactive strategies. In this blog post, we explore the Read More …
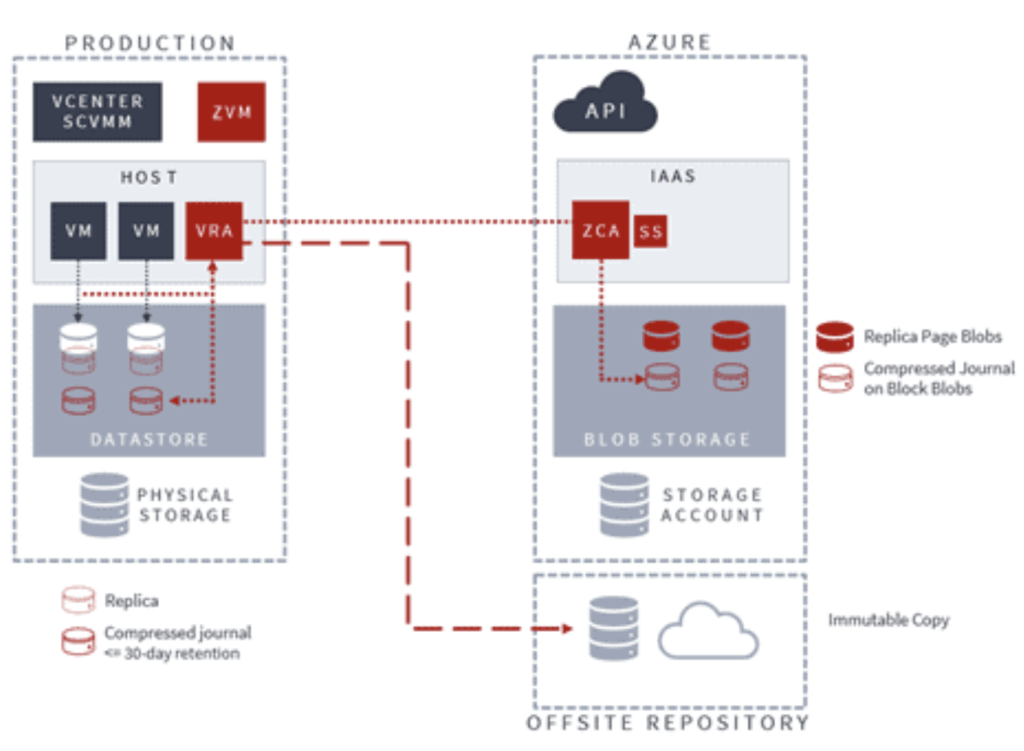
Reading Time: 2 minutesIn the ever-evolving landscape of IT infrastructure, ensuring robust data protection, disaster recovery, and seamless multi-cloud mobility is paramount. Zerto, a leading solution in this domain, offers a comprehensive platform that empowers organizations to safeguard their critical workloads and maintain business Read More …
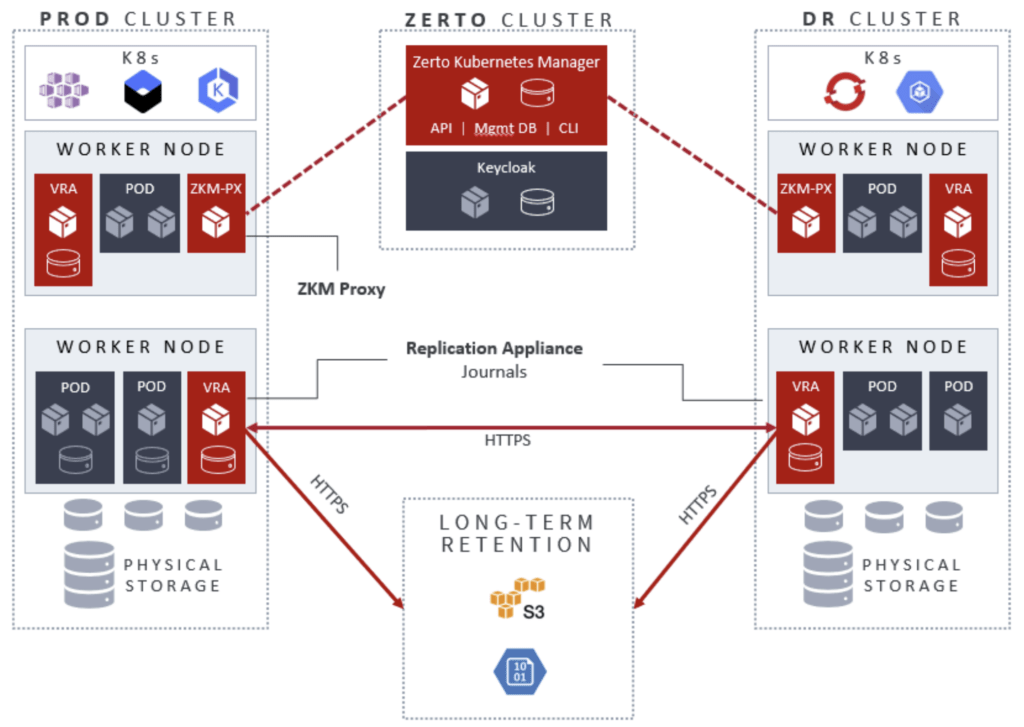
Reading Time: 2 minutesThe purpose of this document is to provide architectural guidance for designing and implementing Zerto for Kubernetes in a production environment. This solution can be optionally paired with a secondary Kubernetes cluster for disaster recovery, with both sites targeting a long-term retention Read More …