
Reading Time: 3 minutesThe decision to build a security platform from open-source components is conditional.
Meeting of Brilliant Syche – IT Pro's Corner

Reading Time: 6 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: June 1, 2024 Location: Dhaka, Bangladesh Version: 1.0 1. The Core Dilemma: Assessor vs. Builder Mindset We are observing worldwide adoption on CISSP Read More …

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: August 8, 2022 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary: DNS as a Strategic Control Plane The Domain Name System (DNS) is no Read More …

Reading Time: 3 minutesStatus: Final Blueprint (Condensed) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: January 6, 2022 Location: Dhaka, Bangladesh Version: 1.0 (Summary) Executive Summary In a landscape of relentless cyber threats, traditional, point-in-time security assessments are Read More …
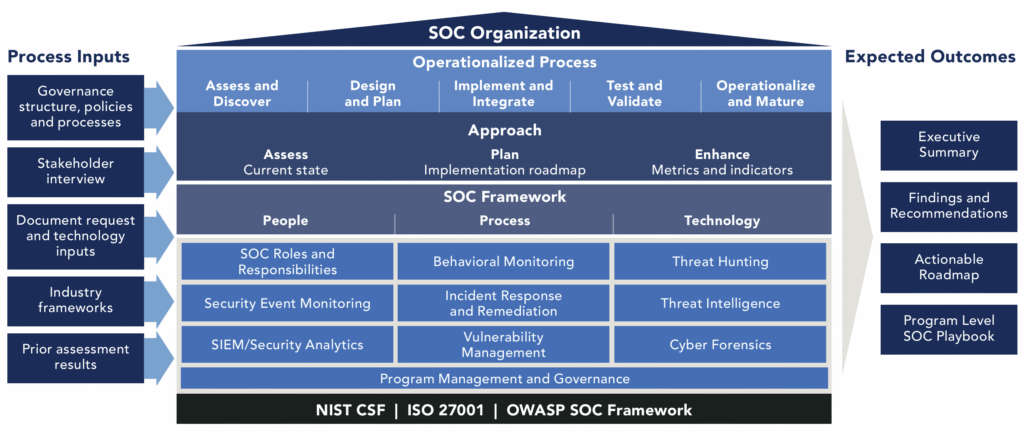
Reading Time: 3 minutesStatus: Final Blueprint Summary Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: April 4, 2024 The SOC as a Strategic Business Enabler The modern Security Operations Center (SOC) has evolved from a technical cost center Read More …

Reading Time: 4 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Version: 1.0 1. Executive Summary: The Illusion of a Single Defense In the modern digital landscape, relying solely on a Distributed Denial-of-Service (DDoS) appliance creates a dangerous false sense of security. Read More …