Reading Time: 4 minutesThis blueprint presents a strategic framework for redressing this imbalance by fusing Artificial Intelligence (AI) with Open-Source Intelligence (OSINT) within a modernized Security Operations Center (SOC)
Meeting of Brilliant Syche – IT Pro's Corner

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: August 8, 2022 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary: DNS as a Strategic Control Plane The Domain Name System (DNS) is no Read More …

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: 2024-07-27 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary In the contemporary multi-cloud enterprise, the ability to grant access across distinct cloud accounts, tenants, and Read More …

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 26, 2024 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary Website defacement is a critical security breach that inflicts significant reputational and financial damage. Read More …

Reading Time: 3 minutesStatus: Summary Blueprint | Author: Shahab Al Yamin Chawdhury | Date: July 2, 2024 | Version: 1.0 1.0 The Strategic Imperative: From Tactical Risk to Crypto-Agility The management of machine identities, secured by digital certificates and Public Key Infrastructure (PKI), Read More …

Reading Time: 4 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: December 12, 2024 Version: 1.0 1. Executive Summary Strategic Imperative The acquisition of VMware by Broadcom has fundamentally altered licensing and product bundling, Read More …
Reading Time: 4 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: October 10, 2022 Version: 1.0 1. Executive Summary The modern enterprise runs on open-source software (OSS), which creates a vast and unmanaged attack Read More …

Reading Time: 3 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: March 26, 2024 Version: 1.0 Executive Summary This document provides a condensed, strategic overview of the “GDPR Implementation & Certification” blueprint. It outlines Read More …

Reading Time: 4 minutesStatus: Final Blueprint Summary Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: 25 July 2025 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary This document addresses the critical gap identified when organizations mistakenly assume their Read More …

Reading Time: 3 minutesStatus: Summary Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: May 23, 2025 Version: 1.0 1. Executive Summary This document summarizes the architectural blueprint for the CMMI Cybermaturity Platform, an enterprise solution designed to Read More …
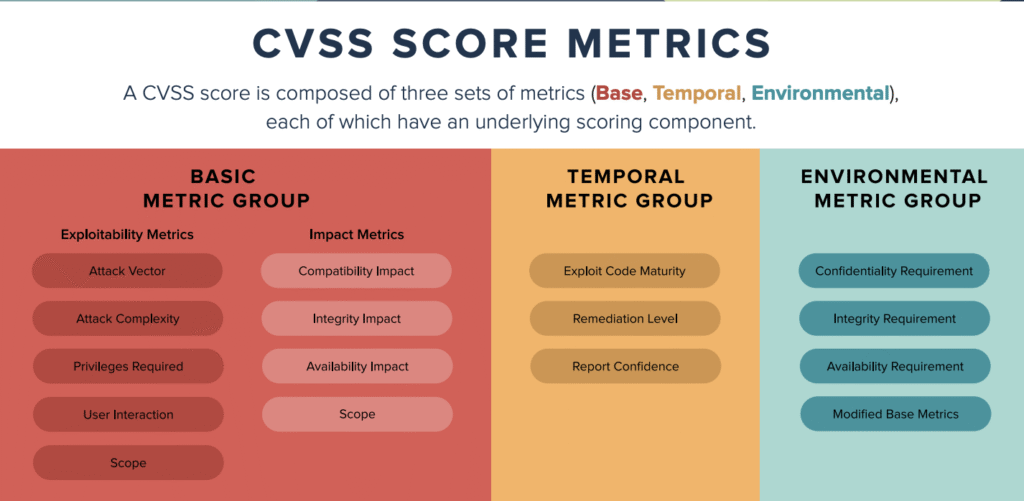
Reading Time: 3 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 2, 2024 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary: Moving Beyond CVSS Modern enterprises are overwhelmed by a “prioritization paradox,” where a flood Read More …

Reading Time: 3 minutesStatus: Final Blueprint (Condensed) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: January 6, 2022 Location: Dhaka, Bangladesh Version: 1.0 (Summary) Executive Summary In a landscape of relentless cyber threats, traditional, point-in-time security assessments are Read More …
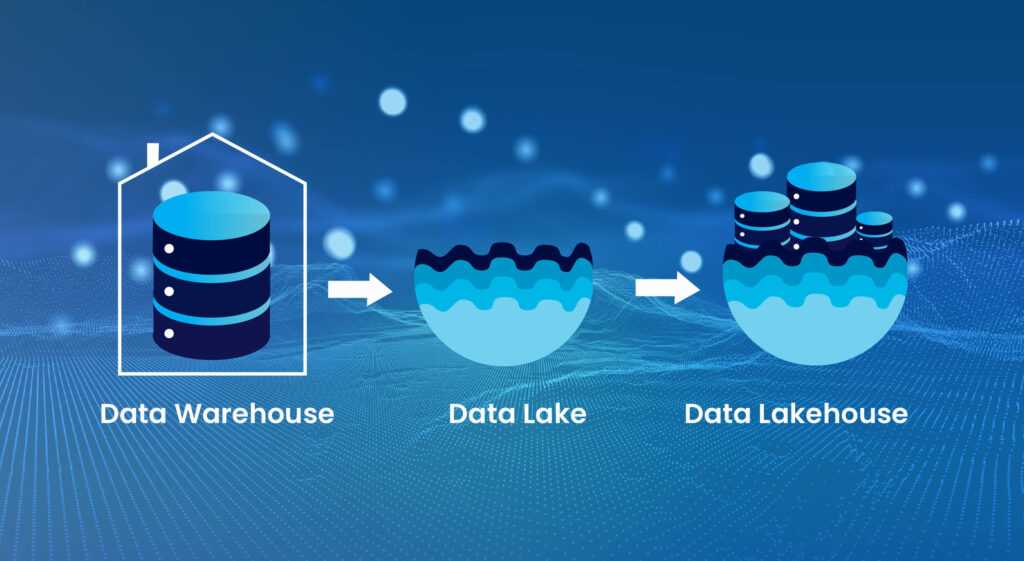
Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: October 26, 2023 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary The Data Lakehouse paradigm marks a critical evolution in enterprise data architecture, merging the Read More …
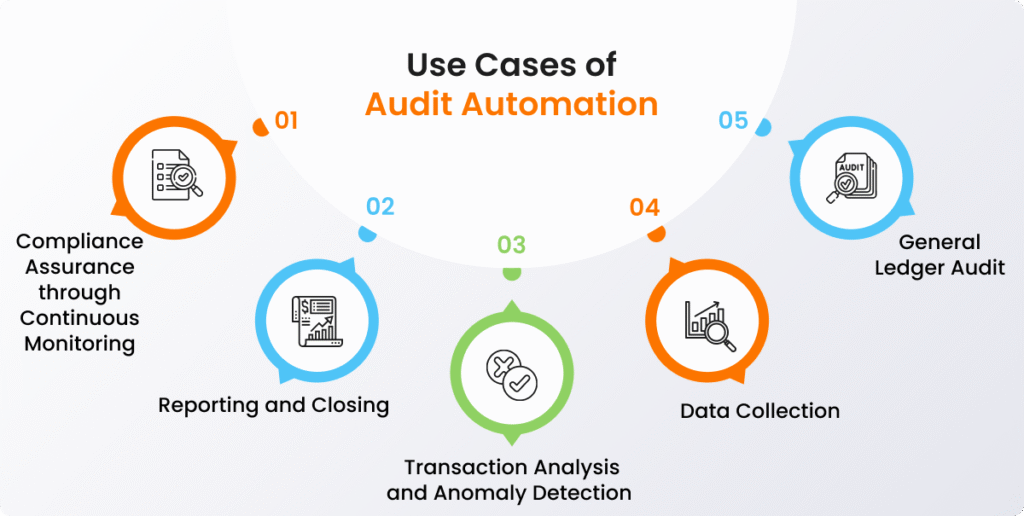
Reading Time: 5 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: December 9, 2024 Location: Dhaka, Bangladesh Version: 1.0 I. Executive Summary The internal audit function is undergoing a significant transformation, driven by complex business Read More …

Reading Time: 3 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: February 2, 2025 Location: Dhaka, Bangladesh Version: 1.0 (Summary) 1. Executive Summary Application Programming Interfaces (APIs) are the central nervous system of the Read More …
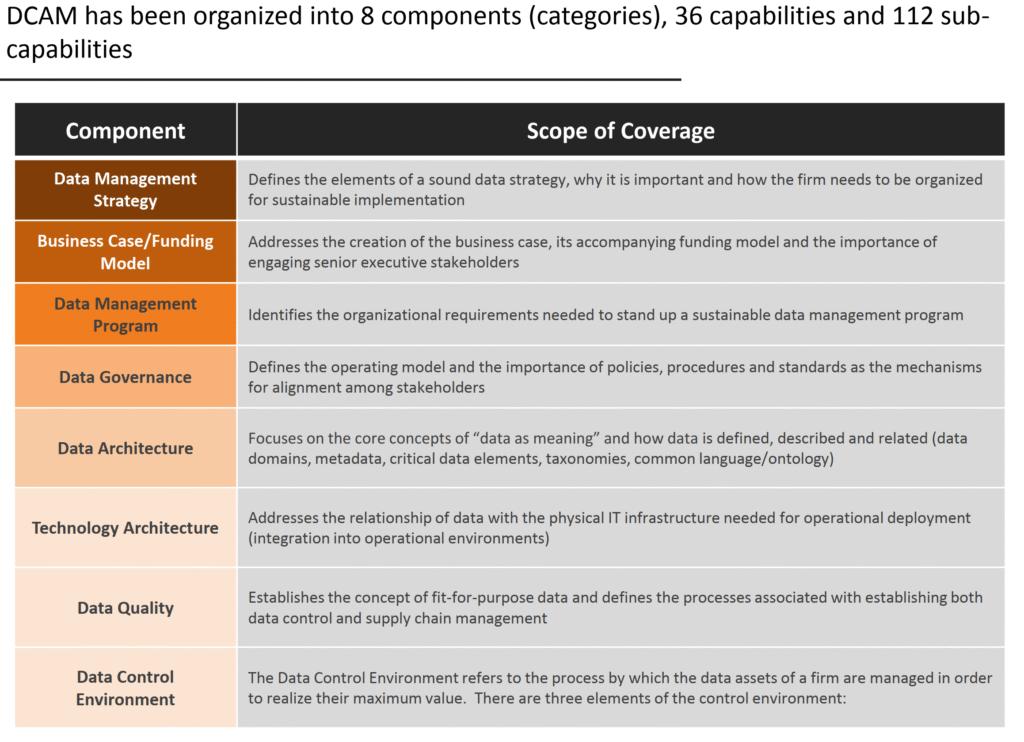
Reading Time: 3 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultancy Group Version: 1.0 Date: July 26, 2024 1. The Strategic Imperative In the modern digital economy, data is a primary strategic asset. The ability to manage, govern, Read More …

Reading Time: 4 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: October 4, 2024 Location: Dhaka, Bangladesh Version: 1.0 (Summary) 1. Executive Summary: The Strategic Imperative for Software-Defined Resilience The function of data protection Read More …
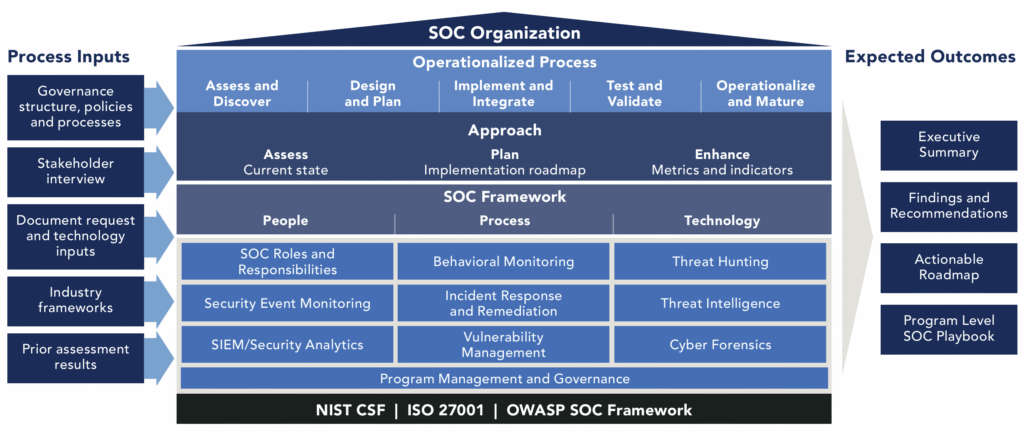
Reading Time: 3 minutesStatus: Final Blueprint Summary Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: April 4, 2024 The SOC as a Strategic Business Enabler The modern Security Operations Center (SOC) has evolved from a technical cost center Read More …
Reading Time: 3 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 24, 2025 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary: The Agentic Enterprise is Here The enterprise is at a pivotal moment, Read More …
Reading Time: 3 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: February 6, 2024 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary Phishing has evolved from a nuisance into a primary and financially devastating Read More …
Reading Time: 3 minutesStatus: Summary Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 24, 2025 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary The modern enterprise faces a critical paradox: the need to defend against costly Read More …

Reading Time: 3 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 23, 2025 Location: Dhaka, Bangladesh Version: 1.0 1. The Proactive Imperative In the modern threat landscape, organizations must operate under the assumption Read More …

Reading Time: 4 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Version: 1.0 1. Executive Summary: The Illusion of a Single Defense In the modern digital landscape, relying solely on a Distributed Denial-of-Service (DDoS) appliance creates a dangerous false sense of security. Read More …
Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: September 10, 2023 Version: 1.0 Executive Summary The modern software development environment has evolved into a distributed, cloud-native, and AI-augmented ecosystem, fundamentally changing the Read More …
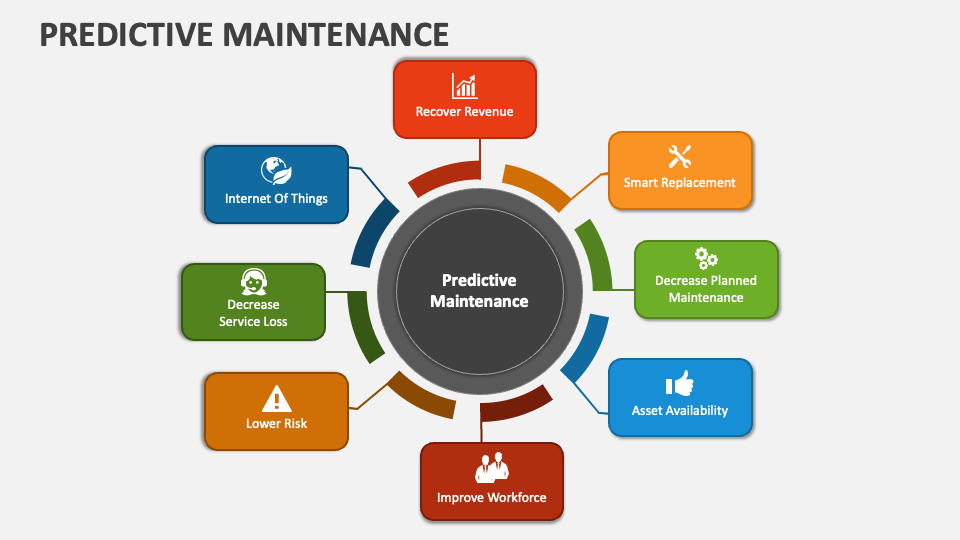
Reading Time: 3 minutesStatus: Summary of Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: October 9, 2024 Version: 1.0 1. The Challenge: The Predictive Maintenance Paradox For years, traditional predictive maintenance (PdM) based on machine learning Read More …

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: May 4, 2024 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary Modern enterprises face a paradox: a landscape of abundant cybersecurity frameworks has led Read More …

Reading Time: 3 minutes1.0 Purpose and Mandate This Security Program Aggregate (SPA) document establishes the formal, high-level governance framework for the organization’s security operations. It serves as the central charter, summarizing the policies and principles that are implemented through the comprehensive suite of Read More …

Reading Time: 5 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: August 28, 2024 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary This blueprint provides a strategic framework for developing Security Operations Center (SOC) playbooks to Read More …
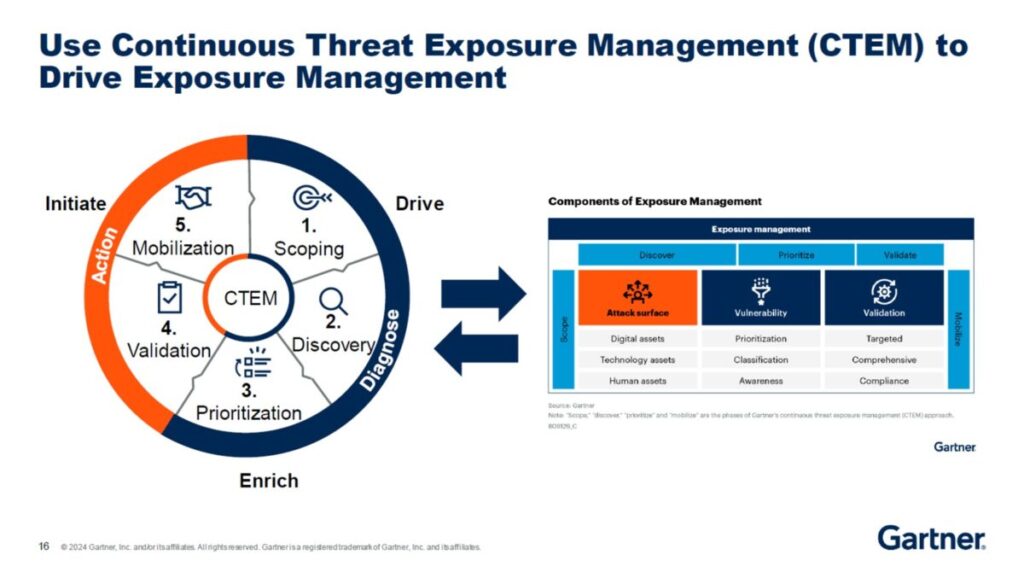
Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 23, 2025 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary Continuous Threat Exposure Management (CTEM) marks a strategic evolution from reactive, incident-driven security to Read More …

Reading Time: 4 minutesStatus: Condensed Summary Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: February 9, 2024 Location: Dhaka, Bangladesh Version: 1.0 (Summary) Executive Summary The Information Systems (IS) auditing profession faces a seismic transformation driven by relentless Read More …
Reading Time: 3 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: September 11, 2023 Location: Dhaka, Bangladesh Version: 1.0 (Summary) Page 1: Strategic Overview & Core Differences 1. The Core Dichotomy: Automated Hygiene vs. Read More …

Reading Time: 5 minutesExecutive Summary The role of the Chief Information Security Officer (CISO) is at a critical inflection point. The immense pressure of the position has created a “Crisis of Command,” where ego-driven leadership fosters a toxic cycle of team burnout, high Read More …

Reading Time: 3 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: October 9, 2024 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary This document addresses the strategic question of whether Internet Service Providers (ISPs) should Read More …
Reading Time: 4 minutesExecutive Summary The central thesis that IT/IS personnel lack the personal drive to upskill is a fundamental misdiagnosis. The core issue is not a failure of individual will but a failure of organizational design. While IT professionals are highly motivated Read More …

Reading Time: 5 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: September 23, 2023 Location: Dhaka, Bangladesh Version: 1.0 1.0 Executive Summary: Beyond Consolidation Unified virtual machine (VM) management has evolved from simple hypervisor consolidation Read More …

Reading Time: 5 minutesThe Enterprise Control Imperative In the modern enterprise, Information Technology General Controls (ITGCs) and IT Application Controls (ITACs) are the bedrock of financial reporting integrity and operational stability. Their effective implementation and auditing are critical for regulatory compliance, particularly with Read More …

Reading Time: 4 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 22, 2024 Version: 1.0 The Strategic Imperative & Modern Architectural Blueprints The Strategic Imperative: Business-Driven Design The modern enterprise network is not Read More …

Reading Time: 5 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: April 22, 2023 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary: An Enterprise-Level Risk Ransomware has evolved from a niche cybersecurity issue into a fundamental Read More …
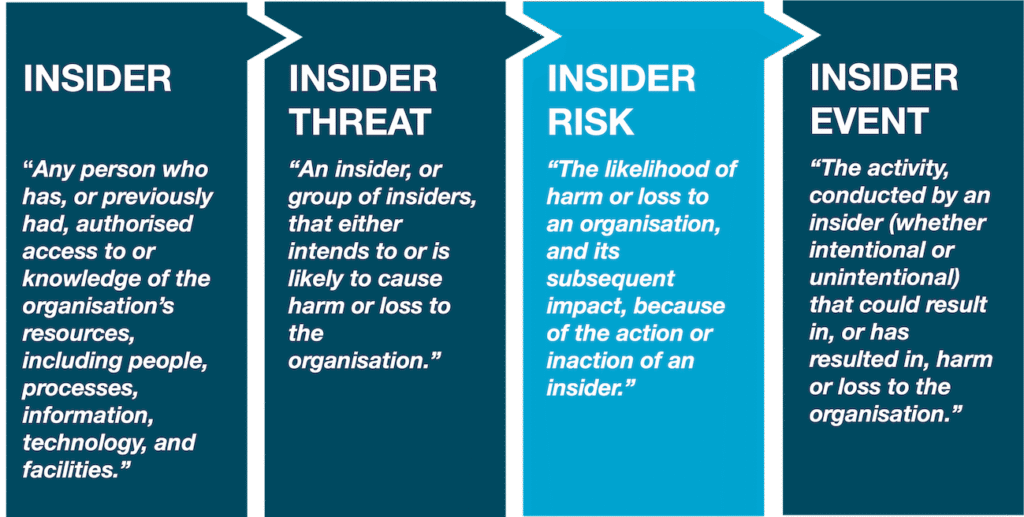
Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 21, 2024 Location: Dhaka, Bangladesh Version: 1.0 1.0 Executive Summary 2.0 The Evolving Threat Landscape 3.0 Amplified Risk Factors in Hybrid Environments 4.0 Read More …
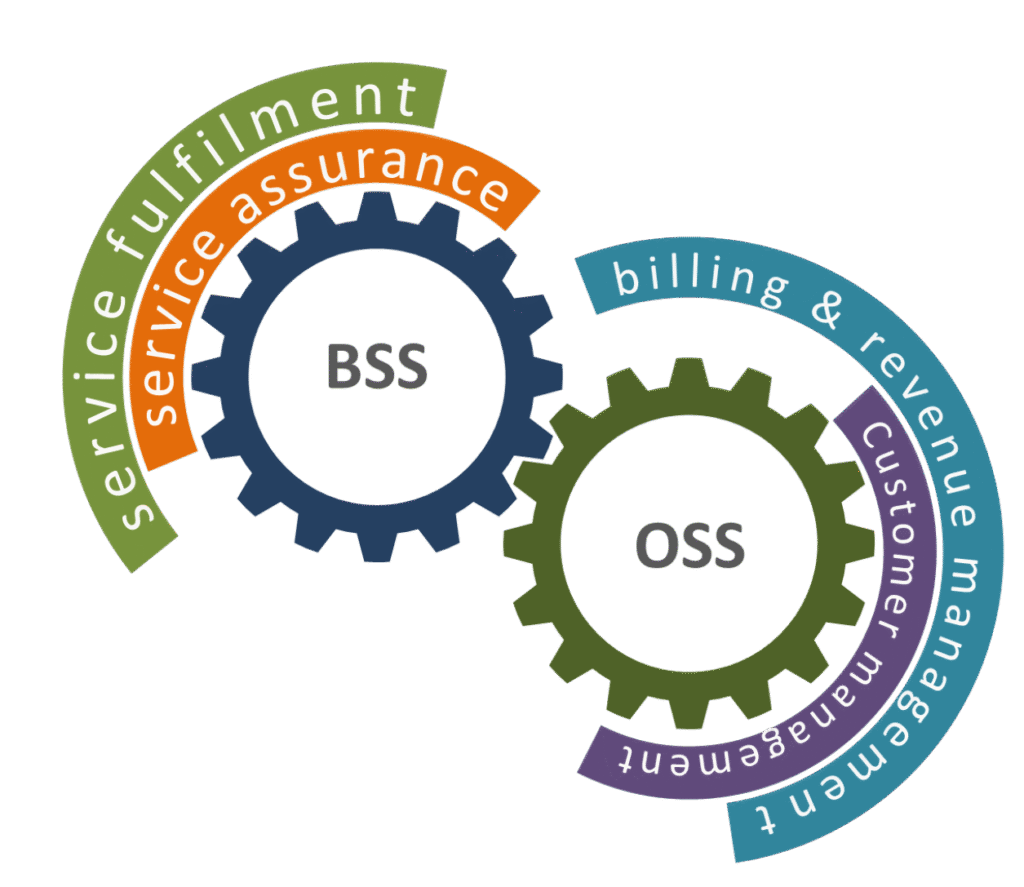
Reading Time: 4 minutes1. Executive Summary This document outlines a comprehensive blueprint for Operations Support Systems (OSS) and Business Support Systems (BSS) requirements within modern enterprise applications. Traditionally the domain of telecommunications, the principles of OSS and BSS are now critical for any Read More …

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 21, 2025 Location: Dhaka, Bangladesh Version: 1.0 1. Executive Summary 2. Deep Dive: Laravel-Specific Concerns for Enterprise Use 3. Deep Dive: MySQL-Specific Concerns Read More …

Reading Time: 6 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: July 22, 2024 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary The enterprise Business Intelligence (BI) landscape is undergoing a seismic shift, driven by the Read More …