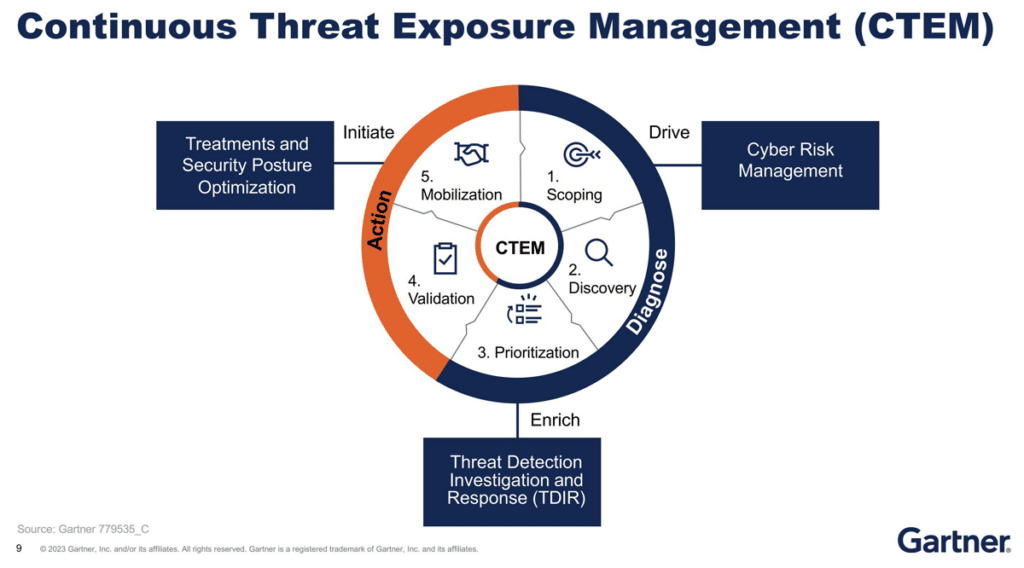
Reading Time: 3 minutesFor years, security teams have relied on separate tools to manage cloud misconfigurations (CSPM), Kubernetes security (KSPM), and sensitive data exposure (DSPM). Meanwhile, Continuous Threat Exposure Management (CTEM) emerged as a programmatic approach to continuously identify, assess, and remediate exposures across the attack surface.