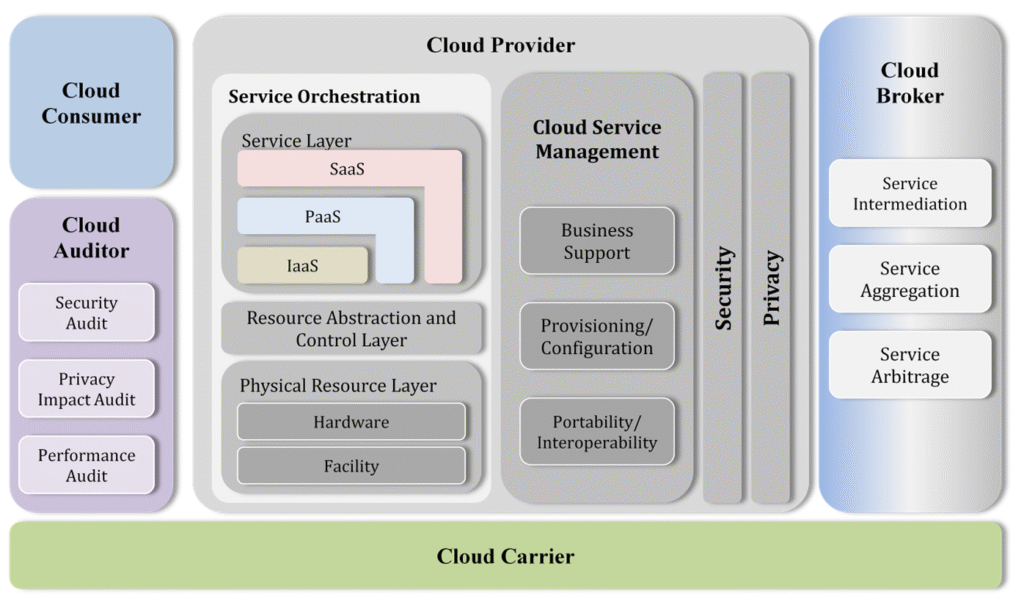
Reading Time: 9 minutesImage Source: https://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication500-292.pdf Cloud computing has become an integral part of modern IT infrastructure, enabling enterprises to achieve scalability, efficiency, and agility. This paper discusses the Cloud Computing Reference Architecture (CCRA), including its key adoption requirements, standard bodies of knowledge Read More …