Reading Time: 4 minutesArtificial Intelligence has crossed a threshold in cybersecurity. It’s no longer just a defensive accelerator — it’s now a fully weaponized capability in the hands of adversaries.
Meeting of Brilliant Syche – IT Pro's Corner

Reading Time: 2 minutesAI-driven tools can craft highly targeted, multilingual phishing emails by scraping OSINT, leaked credentials, and social media profiles. Deepfake voice generators mimic executives’ tone and emotional cues, making human detection far more difficult. Services like PhishGPT+ enable automated spear-phishing campaigns tailored by geolocation, language, and psychological triggers.

Reading Time: 6 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: March 17, 2025 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary The “Implementation Plan – NIST AI RMF” provides a comprehensive roadmap for large enterprises Read More …

Reading Time: 3 minutesThe traditional “castle-and-moat” security model is obsolete, broken by the rise of cloud computing, a hybrid workforce, and the explosion of unmanaged devices. The network perimeter has dissolved, creating a new reality where attackers with compromised credentials can move freely within a supposedly “trusted” internal network.
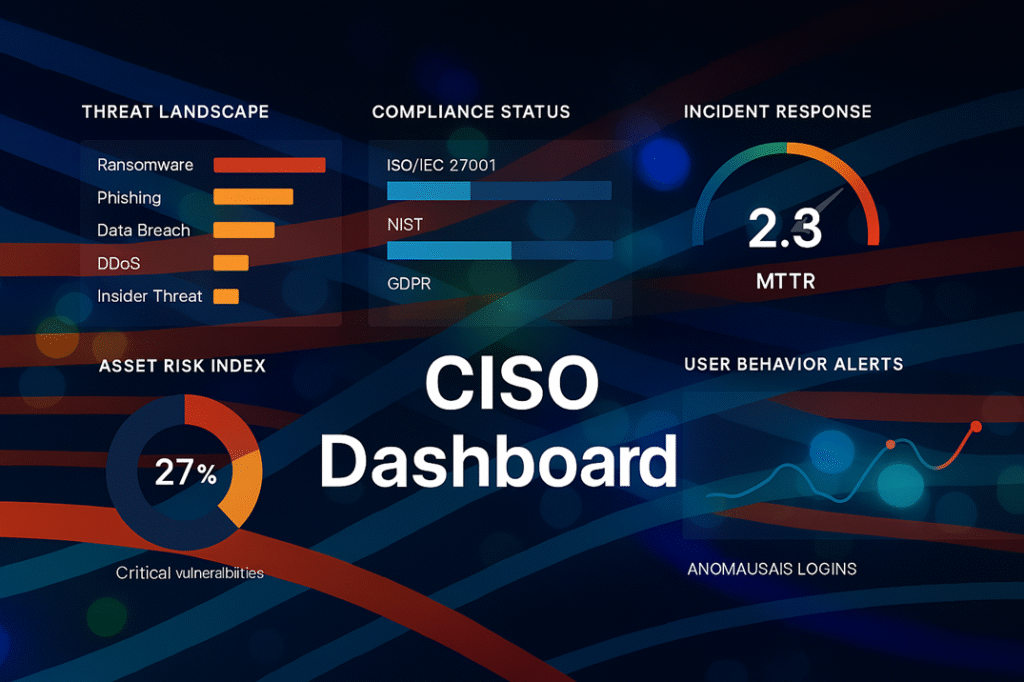
Reading Time: 3 minutesThe modern Chief Information Security Officer (CISO) has evolved from a technical manager into a strategic business leader. In an era of enterprise-wide digital transformation, the CISO’s primary mandate is to architect digital trust, enabling secure business growth while managing cyber risk.

Reading Time: 4 minutesStatus: Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: September 4, 2023 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary: The Data Imperative In the modern economy, data is the central force behind competitive Read More …

Reading Time: 3 minutesStatus: Summary of Final Blueprint Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Date: August 23, 2023 Version: 1.0 1. Introduction & Executive Summary This document provides a condensed overview of the comprehensive AI-specific Incident Response Plan Read More …
Reading Time: 3 minutesStatus: Final BlueprintAuthor: Shahab Al Yamin ChawdhuryOrganization: Principal Architect & Consultant GroupResearch Date: April 9, 2024Location: Dhaka, BangladeshVersion: 1.0 The New Imperative: Securing the AI-Driven Enterprise The integration of Artificial Intelligence (AI) is a present-day reality, creating a new, dynamic, Read More …

Reading Time: 4 minutesStatus: Final Blueprint (Summary) Author: Shahab Al Yamin Chawdhury Organization: Principal Architect & Consultant Group Research Date: 24 May 2024 Location: Dhaka, Bangladesh Version: 1.0 Executive Summary Data Security Posture Management (DSPM) has emerged as a critical strategic response to Read More …